PSA Certified is providing a common language for the industry, allowing the entire value chain to work to the same requirements. The PSA Certified framework offers a standardized approach from initial IoT security design and implementation to security evaluation. It also provides a comprehensive set of free resources to help you build-in best practice security from the beginning of product development. Built by industry experts, it’s been adopted by a rapidly growing ecosystem of silicon vendors, system software providers and device manufacturers.
A Layered Approach to Security
PSA Certified takes a layered approach to IoT security offering certification for all components of a connected device, ensuring that each element has built-in security. Certifications are consumable meaning device manufacturers can leverage expertise from the value chain and build on certified silicon and software. PSA Certified status can also be reused with other security frameworks and evaluation schemes. For example device manufacturers can reuse their certificates to show mappings to regulations and silicon vendors can use their certificates to demonstrate they have a secure Root of Trust suitable for other certification schemes.
Offering Multiple Levels of Silicon Security
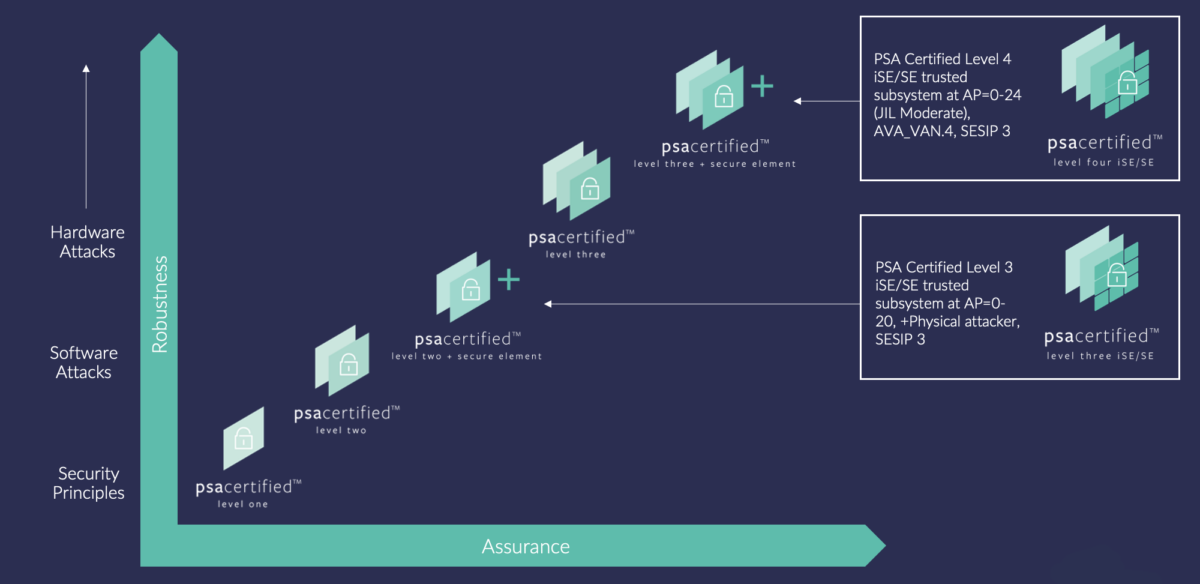
PSA Certified provides the following levels of silicon security robustness to ensure right size security can be built into products:
- PSA Certified Level 1 is available for silicon, system software and endpoint device manufacturers
- PSA Certified Level 2 evaluates the silicon RoT against scalable software attacks
- PSA Certified Level 2+SE includes a Secure Enclave or Secure Element that can protect assets against substantial physical and software attacks
- PSA Certified Level 3 evaluate the silicon Root of Trust against substantial physical and software attacks
- PSA Certified Level 3+SE includes a Secure Enclave or Secure Element that can protect assets against high level of physical and software attacks
- PSA Certified Level 4 iSE/SE is for chip vendors who use an integrated Secure Enclave or external Secure Element that provides a high level of robustness to physical and software attacks
For Silicon
Vendors
For silicon vendors, PSA Certified offers multi-level certification with increasing robustness focused on the silicon’s PSA Root of Trust.
Read MoreFor Software Providers
System software providers can showcase critical security principles with PSA Certified Level 1 and leverage security functions with APIs.
Read MoreFor Device Manufacturers
Device manufacturers can demonstrate best practice security in endpoint devices and development platforms with PSA Certified Level 1.
Read moreBegin your IoT Security Journey Today
PSA Certified has been adopted by world-leading companies all creating a partnership that underpins connected devices and provides real solutions to build trust in the Internet of Things.
Join the Ecosystem That Is Revolutionizing Embedded Security
305
Certifications in our Database
118
Companies with PSA Certified Products

