It is a common misconception that most hacks involve elaborate attempts to compromise an IoT device. Unfortunately, they often occur because simple security measures have been skipped. There are many reasons to be concerned about cybersecurity. Internet of Things (IoT) devices are an attractive target for criminals. They offer a way into someone’s home or organization, and a weakness in a single device can provide access to a larger network or bring down an entire system. Despite this, some product developers aren’t building in baseline security to protect their devices and their data, with simple security measures being overlooked.
In this blog, I’m taking a closer look at the PSA Certified security goals, plus the role of secure storage for connected devices and two partners who can help make secure storage a reality.
Security Requirements for IoT Devices
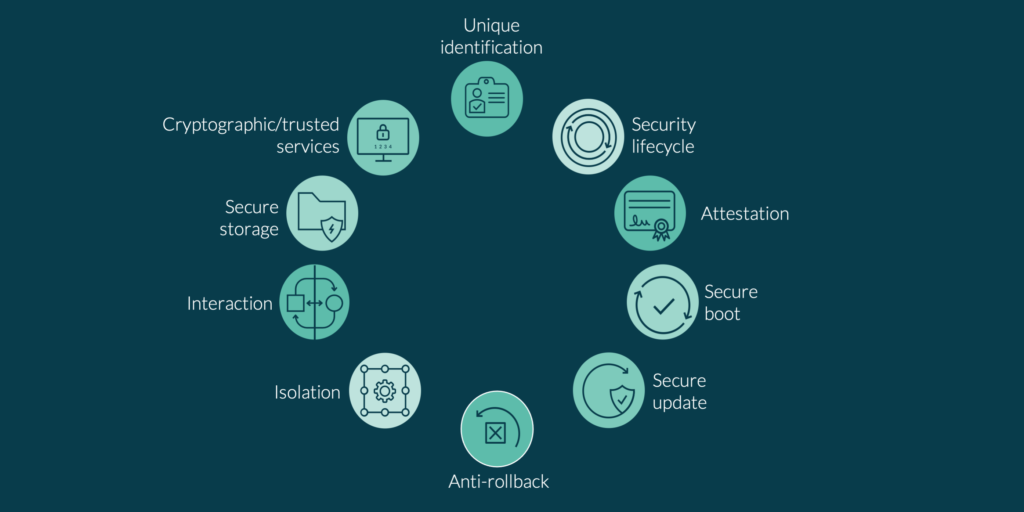
To help ensure trust in the IoT is not eroded by attacks that could easily be prevented, some of the world’s leading security experts have come together to develop a series of security requirements that should be implemented in every connected device. The 10 security goals, as they are called, are a key component of the PSA Certified framework and multi-level certification scheme, and they provide a foundation of security that you can build your device on.
The 10 security goals will help you ensure essential security measures have been taken, and they are flexible enough to be applied to any entity that needs to be trusted, including hardware, software and services. In this blog we discuss the secure storage goal in detail and provide real-world examples from Winbond and Infineon Technologies so you can see how our partners in the ecosystem are implementing the goals to provide a baseline of security for their devices and their customers.
Secure Storage: One of the 10 Security Goals
What makes one storage solution more secure than another? Storage is secure if private data, for example, user or service credentials, or secret keys, are bound to a device to prevent them from being cloned or disclosed outside of the device. This definition of secure storage is included as one of the 10 security goals because of its increasing importance to customers, and industry.
To explain this further, the vast amount of data that is being generated by billions of connected devices will help us run our homes, workplaces, industries and cities of the future more intelligently and efficiently – but only if that data can be trusted. That is because a vulnerability in a device or problems with the data that operators rely on to manage our critical infrastructure and services can have serious consequences.
External storage devices, including Flash, are often used to hold critical system data, securely boot the system, and enable updates. This means they must be secure, if this vital information – and entire systems – are to be protected from cyberattacks.
Below, we showcase two companies that have taken steps to secure their Flash storage solutions in line with the requirements set out in the 10 security goals and had their approach independently assessed by security experts.

Case study 1: Winbond Electronics Corporation
Winbond Electronics Corporation, a global supplier of semiconductor memory solutions, has met the secure storage security requirement with its W75F32W 32Mbit TrustME® Secure Memory Element, a flexible and scalable Flash storage component that can be used by system-on-chip (SoC) and microcontroller unit (MCU) vendors. By doing so, it can demonstrate that its robust approach to security meets the needs of customers that do not want to compromise on security. For example, companies that enable e-payments or cryptocurrency transactions, or that support automotive industry applications.
It has implemented the requirements by:
- Protecting the device’s firmware from remote software attacks
- Utilizing a Root of Trust (RoT), secure boot, firmware resilience and secure over-the-air updates to ensure that only trusted code is loaded on the device
The product has been independently evaluated as part of the PSA Certified scheme at PSA Certified Level 2 Ready for the Secure Store security requirement. That means Winbond can now assure its customers that the RoT has been tested for the secure storage security functional requirement.
“Certification helps us show our customers that we have adopted trusted and proven security solutions that comply with cybersecurity regulations worldwide,” says Winbond’s Secure Flash Product Director, Hung-Wei Chen. “It is also important for the ecosystem. By working with our partners, in our case, silicon vendors, we can help build trust in the IoT by demonstrating that we have taken a holistic approach to security.”
You can find out more about Winbond here and its PSA Certified components here.

Case study 2: Infineon Technologies
Infineon has implemented the secure storage security requirement in its SemperTM Secure NOR Flash device. The technology is being used to power advanced driver assistance systems and autonomous cars; smart meters and medical devices; data center servers; and 5G wireless infrastructure solutions. Suppliers of these equipment must be able to demonstrate that the data being stored on their connected devices can be trusted.
Infineon Technologies has achieved PSA Certified Level 1 requirements which involves documenting best practice against 50 key questions, that questionnaire is then supported by an external lab review. One of the key requirements is using a hardware Root of Trust (RoT) that enables an immutable and unclonable identity to the device. The RoT provides hardware-protected secure storage for keys and certificates, preventing the modification or manipulation of stored data. Semper Secure NOR Flash is the industry first to achieve Functional Safety (ISO 26262 ASIL-B) and PSA Certified security compliance, TCG DICE compliant secure boot and is FIPS 140-2-ready. It has implemented advanced asymmetric key provisioning features with side-channel attack protection.
Sandeep Krishnegowda, Senior Director of Marketing and Applications for Memory Solutions at Infineon Technologies, explains: “Being PSA Certified Level 1 shows our customers we are serious about security and allows them to focus on their designs while we work hard to help them build trust in their devices. It also means our customers are confident in their IoT products’ security and can get to market faster.”
Learn more about Infineon Technologies and its PSA Certified components on our website.

Next Steps
The 10 security goals provide a foundation of security for all connected devices. You can learn more about them on our blog.
