Since the launch of the PSA Certified evaluation scheme in 2019, the PSA Certified founders have been working together to enhance the scheme and ensure it’s the best fit for embedded and IoT applications. The PSA Certified member companies are excited to announce a new level that recognises the use of a Secure Element, with protections against physical attack, that has been integrated as part of the System on Chip’s Root of Trust (PSA-RoT).
Three Reasons Why OEMs Choose to Use a Secure Element
- A typical design pattern for OEMs wanting to build-in hardware security has been to solder a Secure Element (SE) chip alongside the primary System on Chip (SoC). Often these SE chips are delivered with the necessary secret keys and certificates so that they can be built into connected devices and onboarded to popular cloud service providers such as AWS or Microsoft Azure. This pre-provisioning of keys simplifies the device manufacturer’s production process and logistics considerably.
- Most SEs also benefit from advanced protection from physical attack, which is an attractive capability to Cloud Service Providers that care about protecting their secret keys and the integrity of certificate data.
- For Linux-based systems that use applications processor-based chips without integrated non-volatile memory, the SE also becomes a valuable place to store security variables between power cycles, e.g. lifecycle status or anti-rollback counters.
Consequently, adding an SE alongside the SoC is a popular choice.
PSA Certified Level 2 + Secure Element Demonstrates Best Practice Integration

PSA Certified members observed that the soldering of an SE onto the circuit board does not improve security alone. The SE functionality needs to be integrated correctly with the SoC, it’s software and the Cloud Service Provider’s (CSPs) remote software to perform essential functions such as authentication. Additionally, the wires between the SE and the SoC represent an easy target for a hacker with physical access. To encourage OEMs and chip vendors to work on best practice integration of the SE and the SoC’s Root of Trust (RoT) functionality, we have developed PSA Certified Level 2 + Secure Element and published the technical documents (PSA Certified Level 2 SESIP Profile and PSA Certified Level 3 RoT Component SESIP Profile) to enable independent lab-based evaluation.
The Relationship Between the Secure Element and the PSA-RoT
PSA Certified Level 2 + Secure Element considers the SE a pre-certified trusted subsystem of the chip’s PSA RoT (see figure 1 below). This enables the SoC vendor to use a pre-certified embedded Secure Element, eSE, as an alternative to a discrete external chip. A chip vendor offering an eSE-based SoC with a PSA Certified Level 2 + Secure Element certification demonstrates that their RoT can protect sensitive assets from substantial physical attack. We believe this will be valuable to OEMs and CSPs who want to identify products which have a level of physical protection for keys and differentiates these solutions from a PSA Certified Level 2 PSA-RoT that focuses on protection from basic software attacks.
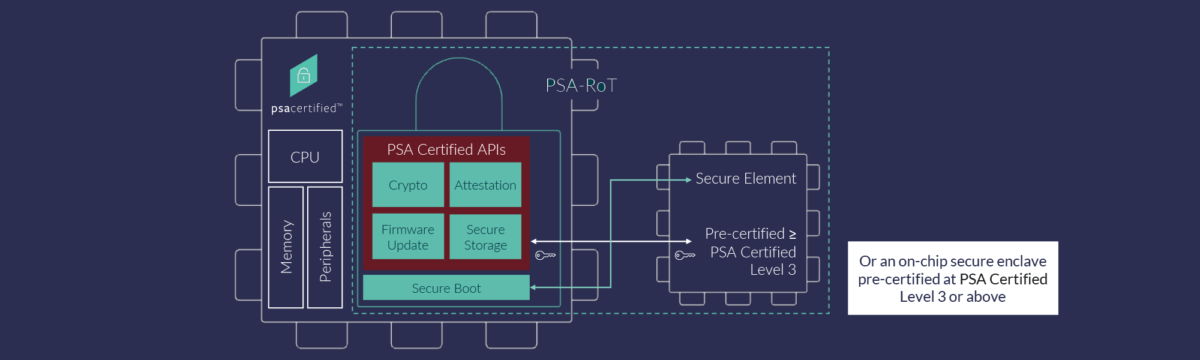
How Does this Differ from PSA Certified Level 3?
PSA Certified Level 3 adds the requirement of physical attacker resistance to the complete set of on-chip PSA-RoT mandatory Security Functional Requirements (SFRs). In contrast, PSA Certified Level 2 + Secure Element focuses on a smaller subset of physically protected security functions provided by the trusted subsystem for example, secure cryptographic operations and secure key storage. PSA Certified Level 2 + Secure Element uses the latest Level 2 SESIP Profile to support the case of using an already certified trusted subsystem via a Level 3 SESIP RoT Component certification.
What are the Benefits for Cloud Service Providers (CSP), OEMs and Chip Vendors?

This new certification has benefits for the entire ecosystem:
- Benefits for Cloud Service Providers: By specifying a PSA Certified Level 2 + Secure Element solution, CSPs can have peace of mind that the SE or eSE storing their credentials is well integrated with the SoC, keeping their data secure.
- Benefits for OEMs: If the PSA Certified Level 2 + Secure Element solution is fully integrated, the OEM can benefit from physical protection to the secret keys and crypto without the cost of another external component. This helps them to offer more robust security to their customers, protecting their brand from more elaborate hacks.
- Benefits for chip vendors: This new level enables chip vendors to validate their security implementation through different paths.
- Chip vendors who already have PSA Certified Level 2 products can extend them to PSA Certified Level 2 + Secure Element with the integration of an external SE, that can extend the market applicability of their product.
- Other chip vendors who cannot achieve a full PSA Certified Level 3 might still be able to offer useful physical protection for keys and crypto and offer a differentiated PSA Certified Level 2 + Secure Element solution that is appreciated by the market.
Quote
Renesas is committed to PSA Certified as the foundation for IoT device security. Renesas’ RA MCU Family has already attained PSA Certified Level 1 and PSA Certified Level 2 certifications and we welcome the launch of PSA Certified Level 2 + Secure Element as next steps. Renesas provide a unique value proposition to customers who require PSA Certified Level 2 + Secure Element certification, having integrated secure element functionality inside our microcontrollers for many years. This integration ensures asset protection and simplifies product development with optimal performance/protection against both physical and remote attacks that target cost-sensitive IoT devices.
Quote
Infineon welcomes the prospect of the new PSA Certified Level 2 certification. It totally aligns with our commitment to make the IoT work by simplifying the integration and delivery of security – so OEMs can bring reliable products to market – more quickly. ‘PSA Certified Level 2 + Secure Element’ brings a number of compelling advantages to OEMs. Enabling scalable security across applications and products, it further simplifies the integration of security into IoT products while also increasing the level of coverage afforded by existing MCU or MPU architectures. Last but not least, precertification offers the added bonus of accelerated time-to-market and lower development costs
